Data Security Practices: Safeguard Your Business Online

Data Security Practices: Safeguard Your Business Online
Do you know how big the risks are today online? Are you ready to keep your business safe from cyberattacks and data breaches? ARK Solvers is your go-to for making sure your data is secure. They help protect your company from these serious threats. https://arksolvers.com/website-security-best-practices/
https://arksolvers.com/website-security-best-practices/
Key Takeaways
- Cybersecurity affects all businesses by causing financial losses, harm to reputations, and fines for not following regulations.
- ARK Solvers says you must use strong security practices to guard against these dangers.
- It’s key to know about data technologies like databases and big data. This knowledge helps keep your data safe.
- Finding and putting tags on important data is the first step to protecting it.
- You must set up ways that control who can see important data. This includes using both technical tools and rules.
Understand Data Technologies and Databases
At ARK Solvers, we know how important it is to understand data technologies and database models. It’s key to protecting your business’s sensitive info. Correct data security protects your private data when using these technologies.
Database Models
Database models decide how data is structured and stored. There are three main models: one-tier, two-tier, and three-tier. Each model has its characteristics like complexity, scalability, and security, and you pick based on your needs.
SQL vs NoSQL Databases
Structured Query Language (SQL) is widely used to talk to databases. It lets users ask questions to database servers in real time. Databases like Oracle, SQL Server, MySQL, and PostgreSQL use SQL. NoSQL databases are for handling unstructured data, making them flexible and scalable for “Big Data.”
Big Data
The size of data keeps growing, making big data management and security harder. Some stores have data that doesn’t fit on one server. They use a storage area network (SAN) to keep all data safe. Protecting big data is very important.
File Systems
File systems manage how unstructured data is stored and accessed. They can be used on different storage types like SSDs or magnetic tapes. The choice of file system depends on the operating system, such as Linux, Windows, or macOS.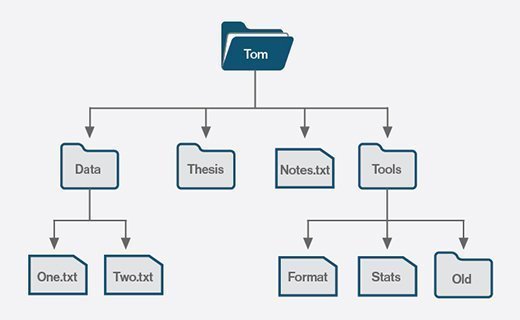
Identify and Classify Sensitive Data
At ARK Solvers, we stress the importance of pinpointing and categorizing sensitive data. This is key to shielding it from dangers. Data discovery and classification form the bedrock of strong data protection.
Sensitive data might be personally identifiable information (PII) like names, home addresses, and more. It could also be confidential business information, including trade secrets. Not protecting this can lead to serious issues like losing customer trust or facing legal penalties.
To protect against these dangers, we recommend a thorough data classification model. This method involves placing your data in categories based on how sensitive it is. For instance, confidential, internal use only, and public. Knowing the sensitivity of your data helps in having the right measures in place, like access controls and employee training.
| Data Classification Level | Examples |
|---|---|
| Confidential Data | Trade secrets, financial information, PII, confidential business information |
| Internal Use Only | Employee payroll information, internal memos, project plans |
| Restricted Data | Customer information, marketing plans, pricing information |
| Public Data | Company press releases, marketing materials |
| Archived Data | Old financial reports, personnel records |
Using a solid data classification system helps reduce the risk of data exposure. It makes sure you follow important laws like the GDPR. This forward-looking approach to managing data is vital for protecting your business from data breaches and other threats.
Create a Data Usage Policy
ARK Solvers underlines making a solid data usage policy. It spells out who can access data, when they can do so, and how it’s used. This setup helps teams follow rules and avoid breaking them.
The policy also says how to treat sensitive info in the office. It tells who can do what with data, like just reading it or changing it. Everyone should only see or change what they need for their job. This keeps things secure by giving the least permission needed.
Then, it explains what happens if someone goes against the rules. This includes using data without permission or not handling it right. Clear rules and outcomes make everyone behave and keep data safe. It also makes sure the policy stays up to date with the law.
| Key Components of a Data Usage Policy | Description |
|---|---|
| Data Classification | Clearly define the different levels of data sensitivity (e.g., public, internal, confidential, restricted) and the appropriate handling procedures for each. |
| Access Controls | Establish guidelines for granting, monitoring, and revoking data access based on an individual’s role and responsibilities. |
| Acceptable Use | Outline permissible and prohibited data usage activities, such as sharing, storing, or processing sensitive information. |
| Incident Response | Define the procedures for reporting and responding to policy violations, including the escalation process and disciplinary actions. |
| Compliance Requirements | Ensure the policy aligns with relevant compliance regulations, such as GDPR, HIPAA, or industry-specific standards. |
Making a strong data usage policy helps keep important info safe. It makes everyone act responsibly with data.
Implement Access Controls
Having strong access controls is key to securing data. At ARK Solvers, we stress using both administrative and technical controls. They help keep sensitive data out of the wrong hands, preventing data breaches.
Administrative Controls
Administrative controls are about rules, procedures, and how people use information. They work on the idea of giving just enough access to do a job. This lowers the chances of data leaks. It involves managing user rights, checking access, and handling when employees leave.
Teaching good password habits and access rules can reduce mistakes that lead to more risks. Having one place to manage access and automatic updates to users’ accounts makes things run smoother. This makes it easier to change rules fast when needed.
Technical Controls
Technology can also be used to control access. Things like firewalls, access lists, and MFA add layers of security. They make it harder for outsiders to get to important data.
RBAC makes it easier to match job roles with what they can access, which improves how things run and keeps data safer. Controls that look at where, what device, or how someone is trying to get in, also step up security by adjusting rules to the situation.
Having up-to-date user lists, watching who gets into what, and checking regularly for issues are vital. This helps in finding and fixing any spots where the security might not be tight enough.
For companies using a lot of cloud tools, linking these together in the access system is critical. It helps keep everything safe and the data of the company well protected.
| Access Control Approach | Description | Typical Use Cases |
|---|---|---|
| Discretionary Access Control (DAC) | Privileges are assigned based on rules specified by individual users or user groups. | Common in desktop operating systems like Windows and macOS. |
| Mandatory Access Control (MAC) | Access permissions and restrictions are enforced based on hierarchical security levels. | Prevalent in government and military organizations. |
| Rule-Based Access Control (RuBAC) | Access is controlled by a set of predefined rules, often used with networking equipment. | Networking devices, such as firewalls and routers. |
| Role-Based Access Control (RBAC) | Access privileges are determined by the user’s assigned role or position within the organization. | Widely used in enterprise-level applications and systems. |
Take Stock: Know Your Data
At ARK Solvers, understanding your data is key. We help you learn about your business’s data. You’ll know where it’s from and how it goes through your company. This knowledge is vital for strong data security.
Identify Data Sources
First, find all the places your business’s data comes from. This could be websites, outside workers, service hotlines, and inside systems. You should look at data about customers, employees, and any private info that might get stolen. This info includes things like Social Security numbers or credit card details.
Understand Data Flow
Then, you map the data’s journey in your company. See how it’s collected, saved, used, and finally deleted. You need to know how it moves between systems and what happens to it. Knowing this helps find and fix weak points. And, it makes sure you follow the rules.
Assess Legal Requirements
Keeping up with laws is crucial for data safety. Acts like the Gramm-Leach-Bliley Act and the Fair Credit Reporting Act set the rules. The consequences for not following are big. For example, Meta got fined $1.3 billion for breaking GDPR rules. Knowing your legal duties helps protect your business and its data.
Scale Down: Keep Only What You Need
At ARK Solvers, we urge businesses to think about what data they collect and keep. We suggest only keeping what’s essential for customers and employees. This can greatly lower the dangers of too much data being out there or potential breaches.
Minimize Data Collection
Stopping yourself from collecting more data is key. Look closely at how your business runs. Then, choose the least amount of customer and employee info you need. Never collect things like Social Security numbers or bank details if you don’t have to.
Develop a Records Retention Policy
Make a solid records retention policy that shows how long you should keep different kinds of data. Keep it up to date with laws like the Gramm-Leach-Bliley Act and the Fair Credit Reporting Act. And after data isn’t needed, make sure to get rid of it safely.
| Key Principle | Description |
|---|---|
| Data Minimization | Only hold onto what you need from customers and employees. This lowers the chance of too much data getting out. |
| Records Retention Policy | Set and keep up with a policy for how long to save data. Make sure to get rid of it safely when it’s time. |
Data Security Practices
At ARK Solvers, we know that keeping your data safe is important. We use many methods to protect your information, such as physical security and training our team. We also keep an eye on how our partners handle data security.
Physical Security Measures
Protecting your office is key to keeping data safe. We set up things like fingerprint scanners and security cameras. Getting rid of old hard drives and papers safely also stops data from getting out.
Electronic Security Measures
Online, we use many layers of security to keep bad guys out. This means using special codes to hide data and making sure only the right people can get in. We always watch our systems to find any weird activities fast.
Employee Training
People can sometimes make mistakes that lead to data leaks. That’s why we train everyone on how to keep data safe and what to do if something goes wrong. We educate them on how to follow the rules that keep our data protected.
Third-Party Vendor Management
Outside partners are part of the security puzzle too. We help our clients make sure those partners also work hard to protect data. This means checking on them regularly and making sure they sign up to keep data safe with us.
By following these steps, companies can avoid big problems caused by data breaches. At ARK Solvers, we are here to help our clients learn and use the best ways to guard their important data.
Conclusion
ARK Solvers underlines the vital role of data security for businesses to protect vital information. They face a rising danger from cyberattacks. Businesses need to know data tech and identify what’s crucial. They should also control access well and use the top security methods. This way, the chance of data theft drops significantly.
The worldwide market for data security is expected to hit $10.78 billion by 2028. This means businesses must make information security and risk management key to their actions. With a complete data security plan, they can guard against threats. This keeps their main assets safe and earns the trust of customers and stakeholders.
ARK Solvers highlights vital cybersecurity measures like multi-factor checks and keeping systems up to date. They also stress the need for data to be scrambled and for proper security checks. Following these steps helps businesses deal with data security issues and helps them succeed in the future.
FAQ
What are the key data technologies and database models that businesses should understand?
Businesses need to know about SQL and NoSQL databases. They should also grasp big data and file systems. This knowledge is vital for strong data security.
Why is it important to identify and classify sensitive data within a business?
It’s key to spot and label sensitive data for protection. This step helps fend off threats like data breaches.
What should a comprehensive data usage policy include?
The policy must detail who can access data and under what conditions. It covers data access based on its sensitivity. Also, it explains proper data use.
What are the different types of access controls businesses should implement?
Companies need to put in place admin and tech controls for data safety. This includes setting user permissions and using digital and physical barriers to guard info.
Why is it important for businesses to have a thorough understanding of the data they collect and how it flows through the organization?
Understand data’s sources and flow, plus legal data protection needs. This is vital for strong security. It helps keep data safe and follow laws.
How can businesses scale down the amount of sensitive data they collect and retain?
To lessen data, companies should only keep what’s necessary. Then, they need a plan to delete unneeded data safely. This approach is known as data minimization.
What are the key components of comprehensive data security practices?
To ensure data security, businesses should use physical and digital measures. They must train employees and manage third-party security well. These steps are all crucial.